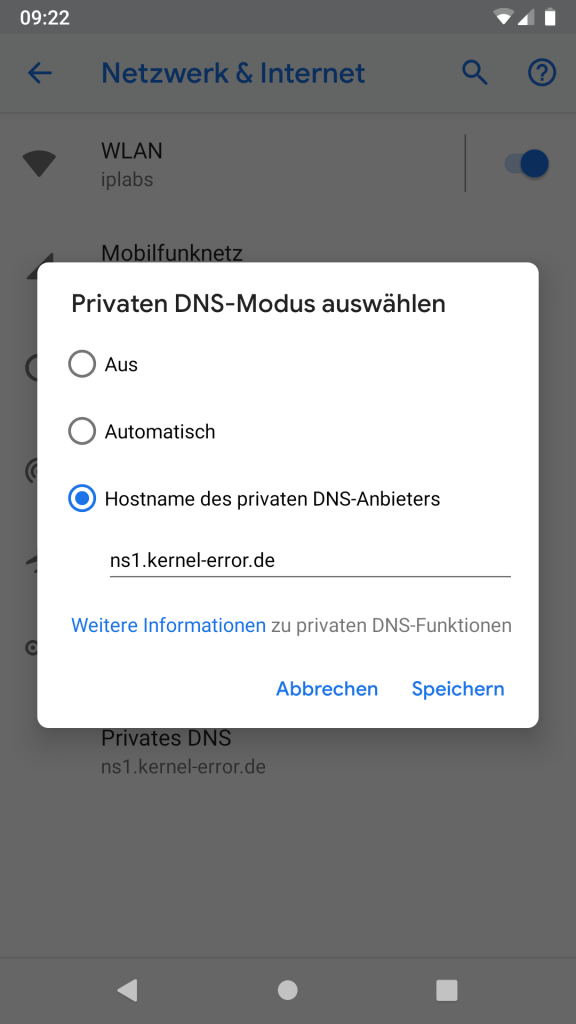
Ihr erinnert euch an meine Ankündigung über TLS an meinem DNS vor ein paar Tagen? RFC 7858 – DNS over Transport Layer Security
Bei mir ist inzwischen recht oft die Frage nach dem „Wie“ angekommen. Nun ich habe dafür stunnel benutzt. stunnel ist nicht speziell für DNS sondern ist ein Stück Software welches sich vor Dienste schalten lässt die keine oder eine schlechte Implementierung für SSL/TLS haben. Eine komplett stumpfe Konfiguration um zu testen würde zum Beispiel auf einem FreeBSD wie folgt aussehen:
/usr/local/etc/stunnel/conf.d/dnstls.conf
[dns4]
accept = 853
connect = 5.9.24.235:53
cert = /usr/local/etc/stunnel/ssl/dns.crt
key = /usr/local/etc/stunnel/ssl/dns.key
CAfile = /usr/local/etc/stunnel/ssl/ca.crt
[dns6]
accept = :::853 connect = 5.9.24.235:53
cert = /usr/local/etc/stunnel/ssl/dns.crt
key = /usr/local/etc/stunnel/ssl/dns.key
CAfile = /usr/local/etc/stunnel/ssl/ca.crt
So gestartet lässt sich eine TLS Verbinung zu Port 853 aufbauen und stunnel schiebt dann alles einfach weiter an den Bind auf Port 53. Ob eine SSL/TLS Verbindung aufgebaut werden kann testet man am besten mit openSSL: openssl s_client -connect ns1.kernel-error.de:853 -showcerts Ich werfe weiter unten mal den kompletten Output in den Post…
Um eine komplette DNS Abfrage über TLS zu prüfen nutze ich gerne getdns_query. Dieses ist bereits in den FreeBSD Ports. Ein Test würde wie folgt aussehen: getdns_query @5.9.24.235 -s -a -A -l L www.kernel-error.de AAAA die Option „-l L“ weißt getdns_query dabei an es per TLS zu probieren. Auch hier werde ich den kompletten Output weiter untem im Post zeigen.
Der versprochene openSSL Output
kernel@s-meer-bsd ~> openssl s_client -connect ns1.kernel-error.de:853 -showcerts
CONNECTED(00000003)
depth=2 C = BE, O = GlobalSign nv-sa, OU = Root CA, CN = GlobalSign Root CA
verify return:1
depth=1 C = BE, O = GlobalSign nv-sa, CN = AlphaSSL CA - SHA256 - G2
verify return:1
depth=0 OU = Domain Control Validated, CN = *.kernel-error.de
verify return:1
---
Certificate chain
0 s:/OU=Domain Control Validated/CN=*.kernel-error.de
i:/C=BE/O=GlobalSign nv-sa/CN=AlphaSSL CA - SHA256 - G2
-----BEGIN CERTIFICATE-----
MIIIVjCCBz6gAwIBAgIMKHSoWgqp4f0QDMWoMA0GCSqGSIb3DQEBCwUAMEwxCzAJ
BgNVBAYTAkJFMRkwFwYDVQQKExBHbG9iYWxTaWduIG52LXNhMSIwIAYDVQQDExlB
bHBoYVNTTCBDQSAtIFNIQTI1NiAtIEcyMB4XDTE3MDMxMDEwNTI1MloXDTE4MDMx
MTEwNTI1MlowPzEhMB8GA1UECxMYRG9tYWluIENvbnRyb2wgVmFsaWRhdGVkMRow
GAYDVQQDDBEqLmtlcm5lbC1lcnJvci5kZTCCAiIwDQYJKoZIhvcNAQEBBQADggIP
ADCCAgoCggIBAMtVm/TykTvxvwZN0h6H2YeIeu4G+scVCb+kxxa8Jrua7DuLchjm
05wj6zPTe+2opDNNeZ6T5/ISSKczUQO4p+ttxFzl8OGA8FaZe4Qc9FNYdzY35w2d
oMgpTpsO+xTEdLHbXcNvEdFXg/8vyKS5y9Ddp8mSvz/Mt04rj2sjXGWwV00ImDQ1
DHBEuNuvFsnyaXQkDXeC3bA+2EkuVIcFcviQT5At88CDLkP8ygJsD3iDudnVeEJZ
N1AFnjN/qQksjKvT5V75R7GcIhA0a6lC56iBmEykht8YdPy63940hYmO4Ug17p68
7uiPZKUsFkGmYchbkiw5KLTck6VVv9b5Z+lFfIQcfBf5blmaUkQQ8CP3yXXajmfP
3KqJu5c+M3OW9evFiE+z7ihtKVtOHQS86z0ijvSNaCfj9OWQKXhBzBzdEGTogC7n
Iq8YYjveRQ+ExffM+RY3xaqMc1368tUx6ir+0LdGiqgzDC5OcWPqRTNobeTfcETz
VCxqgTfVr4tDNTk1+LmRsWKVDuBtG3p/lJEwCU1z6ZP6xmNTBZc1iOuNOJN+CmYW
ZpKaI3F6JPRK4G2Hu4fa0GWjRHSSZYFkyBl520a8fTMGIY8JlfHfx9HVK2fFJ4yP
NxKligKSydphqEG8cyEU/V3oRlgZ7en1HmrWRrIRiWcmWk3qKl/AZk97AgMBAAGj
ggRDMIIEPzAOBgNVHQ8BAf8EBAMCBaAwgYkGCCsGAQUFBwEBBH0wezBCBggrBgEF
BQcwAoY2aHR0cDovL3NlY3VyZTIuYWxwaGFzc2wuY29tL2NhY2VydC9nc2FscGhh
c2hhMmcycjEuY3J0MDUGCCsGAQUFBzABhilodHRwOi8vb2NzcDIuZ2xvYmFsc2ln
bi5jb20vZ3NhbHBoYXNoYTJnMjBXBgNVHSAEUDBOMEIGCisGAQQBoDIBCgowNDAy
BggrBgEFBQcCARYmaHR0cHM6Ly93d3cuZ2xvYmFsc2lnbi5jb20vcmVwb3NpdG9y
eS8wCAYGZ4EMAQIBMAkGA1UdEwQCMAAwPgYDVR0fBDcwNTAzoDGgL4YtaHR0cDov
L2NybDIuYWxwaGFzc2wuY29tL2dzL2dzYWxwaGFzaGEyZzIuY3JsMC0GA1UdEQQm
MCSCESoua2VybmVsLWVycm9yLmRlgg9rZXJuZWwtZXJyb3IuZGUwHQYDVR0lBBYw
FAYIKwYBBQUHAwEGCCsGAQUFBwMCMB0GA1UdDgQWBBSL6GOdfjNSVXP7NNrKRfN/
ZEGEJTAfBgNVHSMEGDAWgBT1zdU8CFD5ak86t5faVoPmadJo9zCCAm0GCisGAQQB
1nkCBAIEggJdBIICWQJXAHUAu9nfvB+KcbWTlCOXqpJ7RzhXlQqrUugakJZkNo4e
0YUAAAFat9mThAAABAMARjBEAiBA/XALdgdBZzdvL20DwfeGUAKVhFAueJG6hIWF
eooeSwIgBAMtgDdRxtSkDbKZdkuT9pul6HlZgGSKBLwHjt08rSAAdgDd6x0reg1P
piCLga2BaHB+Lo6dAdVciI09EcTNtuy+zAAAAVq32ZOaAAAEAwBHMEUCIAwdq+Ma
WZ+v8TuKuwIT9oTHT6mlOuov2brZHNa53o5MAiEAq1ZFktpd5XzJQixebUuaCNKW
dZWUF58tKuB4l7xvGOUAdgCkuQmQtBhYFIe7E6LMZ3AKPDWYBPkb37jjd80OyA3c
EAAAAVq32ZZ1AAAEAwBHMEUCIAUVh0ZRcb/+WRb9F+nn/Jmzvgs/bnLQNwEjBUT1
/t2aAiEAmZWAnrB3RnsCbedw8SOvJk6HsZG67T0fdI96M/Pc47kAdgBWFAaaL9fC
7NP14b1Esj7HRna5vJkRXMDvlJhV1onQ3QAAAVq32Za/AAAEAwBHMEUCIQD92ZOc
1xqff1TJ7gsw/ZGtkvzrjIW6uu/Hu7ZxBKkOgQIgRC0TkK19+m8nUN7KDCqyKsZT
DqUrKE01MuPhx1RnIPMAdgDuS723dc5guuFCaR+r4Z5mow9+X7By2IMAxHuJeqj9
ywAAAVq32ZllAAAEAwBHMEUCIQCPAWIduEfXjVVq+qKHEtoy84Nqm+PsibSk8uXq
ziMziQIgJp3NRvIM8bFtzQe/ZQYBnNv2H3MwZmldaIbV5VcbMOQwDQYJKoZIhvcN
AQELBQADggEBAKmQsE/CjF2nRuqaPZht7EFsQpHzihm+VBA48HDN0Uj9JpObHadg
kxNunKd3K+KNsZP4gwg8Z+LfNAU2smK//Ptq7S/y3ECZTniwLMNx4ogekIuQ9i6a
5zgdN3TpWMV/pu2PEguG/FhDIeIEoC5L7qYAKsSq/4VMexUeVfg3IDbdFH0FGlF7
NRAvfY8KfkvkM6c0VhkAuisnYpt+N3RoXOUlQEbv2qRPikiRnLW4hyms0Y73W5v2
GBA6H66lPIqWTzalY9d1kUVY0N+qz/ZgZhdY0LkeTHG4l+XAyKwa241LHGtDHz7m
7c9LBqS3mXSFvfCL9eU2vzDHkU6cMixjf94=
-----END CERTIFICATE-----
1 s:/C=BE/O=GlobalSign nv-sa/CN=AlphaSSL CA - SHA256 - G2
i:/C=BE/O=GlobalSign nv-sa/OU=Root CA/CN=GlobalSign Root CA
-----BEGIN CERTIFICATE-----
MIIETTCCAzWgAwIBAgILBAAAAAABRE7wNjEwDQYJKoZIhvcNAQELBQAwVzELMAkG
A1UEBhMCQkUxGTAXBgNVBAoTEEdsb2JhbFNpZ24gbnYtc2ExEDAOBgNVBAsTB1Jv
b3QgQ0ExGzAZBgNVBAMTEkdsb2JhbFNpZ24gUm9vdCBDQTAeFw0xNDAyMjAxMDAw
MDBaFw0yNDAyMjAxMDAwMDBaMEwxCzAJBgNVBAYTAkJFMRkwFwYDVQQKExBHbG9i
YWxTaWduIG52LXNhMSIwIAYDVQQDExlBbHBoYVNTTCBDQSAtIFNIQTI1NiAtIEcy
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA2gHs5OxzYPt+j2q3xhfj
kmQy1KwA2aIPue3ua4qGypJn2XTXXUcCPI9A1p5tFM3D2ik5pw8FCmiiZhoexLKL
dljlq10dj0CzOYvvHoN9ItDjqQAu7FPPYhmFRChMwCfLew7sEGQAEKQFzKByvkFs
MVtI5LHsuSPrVU3QfWJKpbSlpFmFxSWRpv6mCZ8GEG2PgQxkQF5zAJrgLmWYVBAA
cJjI4e00X9icxw3A1iNZRfz+VXqG7pRgIvGu0eZVRvaZxRsIdF+ssGSEj4k4HKGn
kCFPAm694GFn1PhChw8K98kEbSqpL+9Cpd/do1PbmB6B+Zpye1reTz5/olig4het
ZwIDAQABo4IBIzCCAR8wDgYDVR0PAQH/BAQDAgEGMBIGA1UdEwEB/wQIMAYBAf8C
AQAwHQYDVR0OBBYEFPXN1TwIUPlqTzq3l9pWg+Zp0mj3MEUGA1UdIAQ+MDwwOgYE
VR0gADAyMDAGCCsGAQUFBwIBFiRodHRwczovL3d3dy5hbHBoYXNzbC5jb20vcmVw
b3NpdG9yeS8wMwYDVR0fBCwwKjAooCagJIYiaHR0cDovL2NybC5nbG9iYWxzaWdu
Lm5ldC9yb290LmNybDA9BggrBgEFBQcBAQQxMC8wLQYIKwYBBQUHMAGGIWh0dHA6
Ly9vY3NwLmdsb2JhbHNpZ24uY29tL3Jvb3RyMTAfBgNVHSMEGDAWgBRge2YaRQ2X
yolQL30EzTSo//z9SzANBgkqhkiG9w0BAQsFAAOCAQEAYEBoFkfnFo3bXKFWKsv0
XJuwHqJL9csCP/gLofKnQtS3TOvjZoDzJUN4LhsXVgdSGMvRqOzm+3M+pGKMgLTS
xRJzo9P6Aji+Yz2EuJnB8br3n8NA0VgYU8Fi3a8YQn80TsVD1XGwMADH45CuP1eG
l87qDBKOInDjZqdUfy4oy9RU0LMeYmcI+Sfhy+NmuCQbiWqJRGXy2UzSWByMTsCV
odTvZy84IOgu/5ZR8LrYPZJwR2UcnnNytGAMXOLRc3bgr07i5TelRS+KIz6HxzDm
MTh89N1SyvNTBCVXVmaU6Avu5gMUTu79bZRknl7OedSyps9AsUSoPocZXun4IRZZ
Uw==
-----END CERTIFICATE-----
---
Server certificate
subject=/OU=Domain Control Validated/CN=*.kernel-error.de
issuer=/C=BE/O=GlobalSign nv-sa/CN=AlphaSSL CA - SHA256 - G2
---
No client certificate CA names sent
Peer signing digest: SHA512
Server Temp Key: ECDH, P-256, 256 bits
---
SSL handshake has read 4014 bytes and written 433 bytes
---
New, TLSv1/SSLv3, Cipher is ECDHE-RSA-AES256-GCM-SHA384
Server public key is 4096 bit
Secure Renegotiation IS supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
SSL-Session:
Protocol : TLSv1.2
Cipher : ECDHE-RSA-AES256-GCM-SHA384
Session-ID: B1956B432DABE228C78E756329A796FA56C9646BE64326F8F96782BD946CCA82
Session-ID-ctx:
Master-Key: 10329FBAE32471FC56D45E0AA0971CF5EB7977F7569AE4079219D9438E7A0F9DA8EC4150D9A074FC0AD8E63E00849047
Key-Arg : None
PSK identity: None
PSK identity hint: None
SRP username: None
Start Time: 1513937385
Timeout : 300 (sec)
Verify return code: 0 (ok)
---
Der versprochene getdns_query Output:
kernel@s-meer-bsd ~> getdns_query @5.9.24.235 -s -a -A -l L www.kernel-error.de AAAA
{
"answer_type": GETDNS_NAMETYPE_DNS,
"canonical_name": <bindata for www.kernel-error.de.>,
"just_address_answers":
[
{
"address_data": <bindata for 2a01:4f8:161:3ec::443>,
"address_type": <bindata of "IPv6">
},
{
"address_data": <bindata for 5.9.24.250>,
"address_type": <bindata of "IPv4">
}
],
"replies_full":
[
<bindata of 0xd3578500000100010003000703777777...>,
<bindata of 0xe9288500000100010003000703777777...>
],
"replies_tree":
[
{
"additional":
[
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns1.kernel-error.de.>,
"rdata":
{
"ipv4_address": <bindata for 5.9.24.235>,
"rdata_raw": <bindata of 0x050918eb>
},
"ttl": 300,
"type": GETDNS_RRTYPE_A
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns2.kernel-error.org.>,
"rdata":
{
"ipv4_address": <bindata for 176.9.109.53>,
"rdata_raw": <bindata of 0xb0096d35>
},
"ttl": 300,
"type": GETDNS_RRTYPE_A
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns3.kernel-error.com.>,
"rdata":
{
"ipv4_address": <bindata for 203.137.119.119>,
"rdata_raw": <bindata of 0xcb897777>
},
"ttl": 300,
"type": GETDNS_RRTYPE_A
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns1.kernel-error.de.>,
"rdata":
{
"ipv6_address": <bindata for 2a01:4f8:161:3ec::53>,
"rdata_raw": <bindata of 0x2a0104f8016103ec0000000000000053>
},
"ttl": 300,
"type": GETDNS_RRTYPE_AAAA
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns2.kernel-error.org.>,
"rdata":
{
"ipv6_address": <bindata for 2a01:4f8:150:1095::53>,
"rdata_raw": <bindata of 0x2a0104f8015010950000000000000053>
},
"ttl": 300,
"type": GETDNS_RRTYPE_AAAA
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns3.kernel-error.com.>,
"rdata":
{
"ipv6_address": <bindata for 2001:310:6000:f::1fc7:1>,
"rdata_raw": <bindata of 0x200103106000000f000000001fc70001>
},
"ttl": 300,
"type": GETDNS_RRTYPE_AAAA
},
{
"do": 0,
"extended_rcode": 0,
"rdata":
{
"rdata_raw": <bindata of 0x>
},
"type": GETDNS_RRTYPE_OPT,
"udp_payload_size": 4096,
"version": 0,
"z": 0
}
],
"answer":
[
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for www.kernel-error.de.>,
"rdata":
{
"ipv6_address": <bindata for 2a01:4f8:161:3ec::443>,
"rdata_raw": <bindata of 0x2a0104f8016103ec0000000000000443>
},
"ttl": 300,
"type": GETDNS_RRTYPE_AAAA
}
],
"answer_type": GETDNS_NAMETYPE_DNS,
"authority":
[
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for kernel-error.de.>,
"rdata":
{
"nsdname": <bindata for ns2.kernel-error.org.>,
"rdata_raw": <bindata for ns2.kernel-error.org.>
},
"ttl": 86400,
"type": GETDNS_RRTYPE_NS
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for kernel-error.de.>,
"rdata":
{
"nsdname": <bindata for ns1.kernel-error.de.>,
"rdata_raw": <bindata of 0x036e7331c010>
},
"ttl": 86400,
"type": GETDNS_RRTYPE_NS
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for kernel-error.de.>,
"rdata":
{
"nsdname": <bindata for ns3.kernel-error.com.>,
"rdata_raw": <bindata for ns3.kernel-error.com.>
},
"ttl": 86400,
"type": GETDNS_RRTYPE_NS
}
],
"canonical_name": <bindata for www.kernel-error.de.>,
"header":
{
"aa": 1,
"ad": 0,
"ancount": 1,
"arcount": 7,
"cd": 0,
"id": 54103,
"nscount": 3,
"opcode": GETDNS_OPCODE_QUERY,
"qdcount": 1,
"qr": 1,
"ra": 0,
"rcode": GETDNS_RCODE_NOERROR,
"rd": 1,
"tc": 0,
"z": 0
},
"question":
{
"qclass": GETDNS_RRCLASS_IN,
"qname": <bindata for www.kernel-error.de.>,
"qtype": GETDNS_RRTYPE_AAAA
}
},
{
"additional":
[
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns1.kernel-error.de.>,
"rdata":
{
"ipv4_address": <bindata for 5.9.24.235>,
"rdata_raw": <bindata of 0x050918eb>
},
"ttl": 300,
"type": GETDNS_RRTYPE_A
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns2.kernel-error.org.>,
"rdata":
{
"ipv4_address": <bindata for 176.9.109.53>,
"rdata_raw": <bindata of 0xb0096d35>
},
"ttl": 300,
"type": GETDNS_RRTYPE_A
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns3.kernel-error.com.>,
"rdata":
{
"ipv4_address": <bindata for 203.137.119.119>,
"rdata_raw": <bindata of 0xcb897777>
},
"ttl": 300,
"type": GETDNS_RRTYPE_A
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns1.kernel-error.de.>,
"rdata":
{
"ipv6_address": <bindata for 2a01:4f8:161:3ec::53>,
"rdata_raw": <bindata of 0x2a0104f8016103ec0000000000000053>
},
"ttl": 300,
"type": GETDNS_RRTYPE_AAAA
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns2.kernel-error.org.>,
"rdata":
{
"ipv6_address": <bindata for 2a01:4f8:150:1095::53>,
"rdata_raw": <bindata of 0x2a0104f8015010950000000000000053>
},
"ttl": 300,
"type": GETDNS_RRTYPE_AAAA
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for ns3.kernel-error.com.>,
"rdata":
{
"ipv6_address": <bindata for 2001:310:6000:f::1fc7:1>,
"rdata_raw": <bindata of 0x200103106000000f000000001fc70001>
},
"ttl": 300,
"type": GETDNS_RRTYPE_AAAA
},
{
"do": 0,
"extended_rcode": 0,
"rdata":
{
"rdata_raw": <bindata of 0x>
},
"type": GETDNS_RRTYPE_OPT,
"udp_payload_size": 4096,
"version": 0,
"z": 0
}
],
"answer":
[
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for www.kernel-error.de.>,
"rdata":
{
"ipv4_address": <bindata for 5.9.24.250>,
"rdata_raw": <bindata of 0x050918fa>
},
"ttl": 300,
"type": GETDNS_RRTYPE_A
}
],
"answer_type": GETDNS_NAMETYPE_DNS,
"authority":
[
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for kernel-error.de.>,
"rdata":
{
"nsdname": <bindata for ns2.kernel-error.org.>,
"rdata_raw": <bindata for ns2.kernel-error.org.>
},
"ttl": 86400,
"type": GETDNS_RRTYPE_NS
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for kernel-error.de.>,
"rdata":
{
"nsdname": <bindata for ns1.kernel-error.de.>,
"rdata_raw": <bindata of 0x036e7331c010>
},
"ttl": 86400,
"type": GETDNS_RRTYPE_NS
},
{
"class": GETDNS_RRCLASS_IN,
"name": <bindata for kernel-error.de.>,
"rdata":
{
"nsdname": <bindata for ns3.kernel-error.com.>,
"rdata_raw": <bindata for ns3.kernel-error.com.>
},
"ttl": 86400,
"type": GETDNS_RRTYPE_NS
}
],
"canonical_name": <bindata for www.kernel-error.de.>,
"header":
{
"aa": 1,
"ad": 0,
"ancount": 1,
"arcount": 7,
"cd": 0,
"id": 59688,
"nscount": 3,
"opcode": GETDNS_OPCODE_QUERY,
"qdcount": 1,
"qr": 1,
"ra": 0,
"rcode": GETDNS_RCODE_NOERROR,
"rd": 1,
"tc": 0,
"z": 0
},
"question":
{
"qclass": GETDNS_RRCLASS_IN,
"qname": <bindata for www.kernel-error.de.>,
"qtype": GETDNS_RRTYPE_A
}
}
],
"status": GETDNS_RESPSTATUS_GOOD
}
Oh und weil ich gerade dabei war… Ich habe direkt ns2.kernel-error.org mit einem gültigen Zertifikat ausgestattet.
Fragen? Dann fragen 🙂